Create an Azure Service Principal for Ansible Tower (AWX)
Scenario
You want to test Azure Provisioning using Ansible Tower (or the Open Source version, AWX) so you’ll need a way to authenticate with Azure.
Solution
An Azure Service Principle will need to be created so that Ansible Tower can authenticate.
Method 1: Azure CLI
- Install the Azure CLI.
- Create an Azure Service Principal called
ansiblewith the passwordMyStrongPassw0rd!az ad sp create-for-rbac --name ansible --password MyStrongPassw0rd! - This will return some JSON like the example below:
{ "appId": "abcd1234-abcd-efff-1234-abcd12345678", "displayName": "ansible", "name": "http://ansible", "password": "MyStrongPassw0rd!", "tenant": "12345678-ab12-cd34-ef56-1234abcd5678" } - The
appIdkey above is referred to as theclient_idfor the Azure Credential in Ansible Tower. - The
passwordkey above is referred to as thesecretfor the Azure Credential in Ansible Tower. - The
tenantkey above is also referred to as thetenantfor the Azure Credential in Ansible Tower. - To show your Azure Subscriptions, run the following
> az account list --output table Name CloudName SubscriptionId State IsDefault ---------- ----------- ------------------------------------ ------- ----------- Free Trial AzureCloud aaaa1111-bbbb-cccc-abcd-aaabbbcccddd Enabled True - Note down your
SubscriptionIdfor later use.
Method 2: Azure PowerShell
- Install the new Azure PowerShell Module:
Install-Module -Name Az -AllowClobber - Create an Azure Service Principal called
ansiblewith the passwordMyStrongPassw0rd!:$servicePrincipleName = 'ansible' $secureString = ConvertTo-SecureString 'MyStrongPassw0rd!' -AsPlainText -Force $azADApplicationParams = @{ DisplayName = $servicePrincipleName IdentifierUris = "http://$($servicePrincipleName)" Password = $secureString } New-AzADApplication @azADApplicationParams -Verbose - This will return an object like this:
DisplayName : ansible ObjectId : 11111111-2222-3333-abcd-12345678abcd IdentifierUris : {http://ansible} HomePage : Type : ApplicationId : abcd1234-abcd-efff-1234-abcd12345678 AvailableToOtherTenants : False AppPermissions : ReplyUrls : {} ObjectType : Application - The
ApplicationIdkey above is referred to as theclient_idfor the Azure Credential in Ansible Tower. - To show your Azure Subscriptions, run the following
Get-AzSubscription Name Id TenantId State ---- -- -------- ----- Pay-As-You-Go aaaa1111-bbbb-cccc-abcd-aaabbbcccddd 12345678-ab12-cd34-ef56-1234abcd5678 Enabled - Note down
Id(Subscription ID) andTenantIdfor later use.
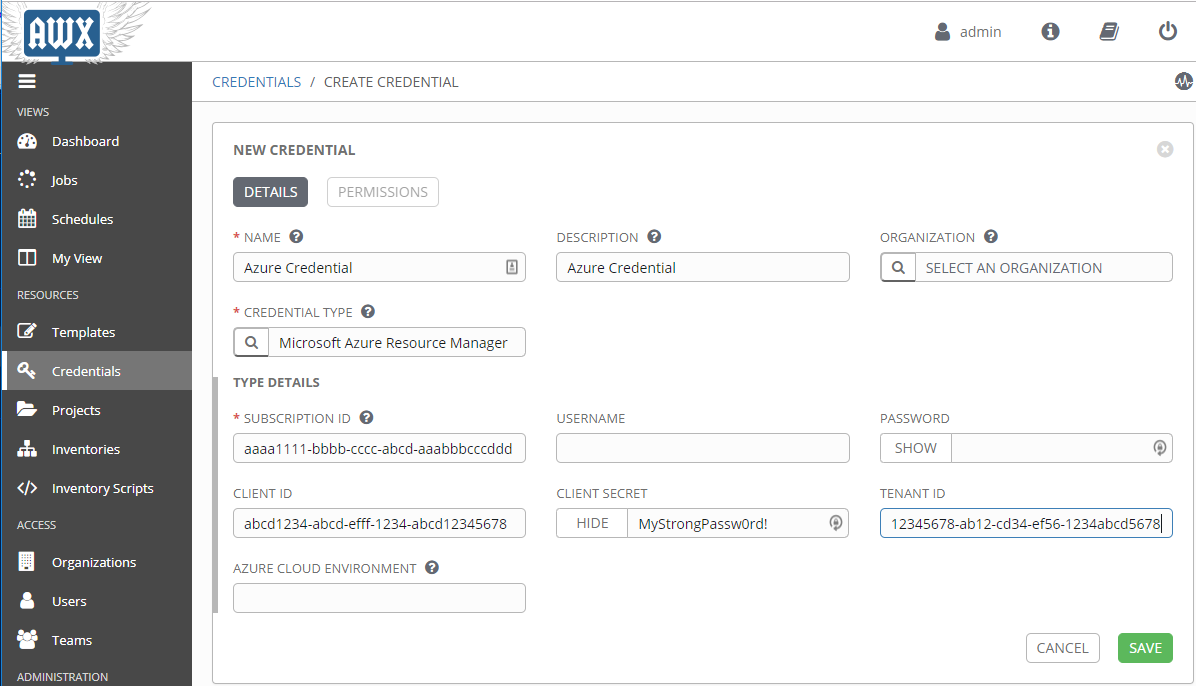
Create an Azure Credential in Ansible Tower (AWX)
- Navigate to the Credentials page, within the Resources menu.
- Create a new Credential and ensure the
CREDENTIAL TYPEfield isMicrosoft Azure Resource Manager. - Enter the previously created values into the
SUBSCRIPTION ID,CLIENT ID,CLIENT SECRET, andTENANT IDfields as shown below:



Leave a comment